- Go to the Privy Dashboard
- Select your app from the App Dropdown in the left sidebar
- Request access to Custom Auth Support in the Integrations > Plugins tab of the Privy dashboard
- Navigate to the JWT Dashboard via User management > Authentication > JWT-based auth
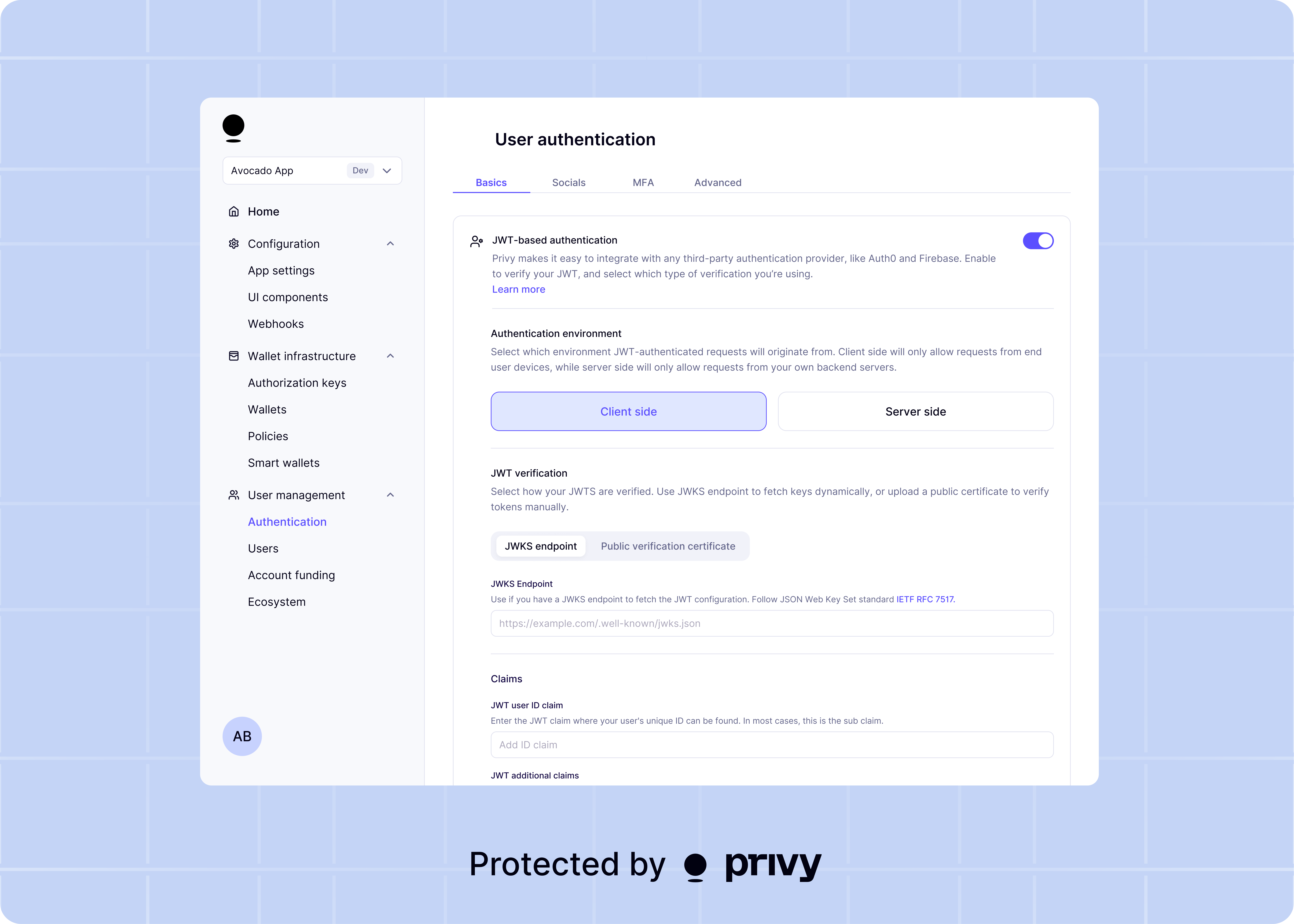
Authentication environment
Choose where JWT-authenticated requests can originate from: client-side (end user devices),
server-side (your backend), or both.
Privy requires a verification key to ensure the JWTs received are valid. Both the token’s signature and its expiration time (claim) are verified to ensure secure access. This verification process helps protect user data and prevents unauthorized access to Privy services.You can provide the verification key in one of two ways:
JWKS Endpoint
JWKS Endpoint
If your provider uses JWKS to sign JWTs, provide a JWKS endpoint URL where Privy can retrieve your auth provider’s JWT public key.
Public Verification Key
Public Verification Key
If your provider uses a single key to sign JWTs, provide the corresponding public key certificate used for verification.
Enter the claim from your user’s JWT that contains the user’s unique ID. In most access tokens and
identity tokens, this is the claim.

